Should your EC2 instance have a public IP and port 22 open so that you can ssh into it from your machine? Answer is no. A very big NOOOO!
Sounds counter inituitive? Not once you understand how instance connectivity works in AWS.
It feels like magic, but it’s just AWS Systems Manager (SSM) at work.
The "Magic" of Zero Open Ports
With SSM Session Manager, you can connect to your instances without any inbound ports open in your Security Groups. None. Nada!
How? Instead of you knocking on the instance's door (Inbound ssh port), the SSM Agent inside the instance reaches out to the AWS SSM service (Outbound) to ask if anyone wants to talk.

Wait, but for that you need the instance to be able to talk to outside world right? So we do need some kind of connectivity. A NAT Gateway then? Not really. With a VPC Endpoint for SSM in the VPC subnet, we can talk to only the ssm service securely and privately.
So EC2 Instance can talk to SSM Service through the VPC Endpoint, AWS bridges that connection securely.
But for this to work, following conditions must be met:
Prerequisites:
VPC Endpoint for SSM : So that we have connectivity between EC2 Instances and the SSM Service.
SSM Agent Installed on the machine : AWS Linux images have them by defauly so you are covered.
IAM Instance Profile attached to the EC2 Instance: So that AWS IAM knows that you are allowing this EC2 Instance to talk to AWS Systems Manager Service.
Thats it! No more allow from 0.0.0.0/0 on Port 22 in your Security Group.
Once you have all the above prerequisites fulfillled, you can seemlessly connect to instance via SSM direct from the browser.
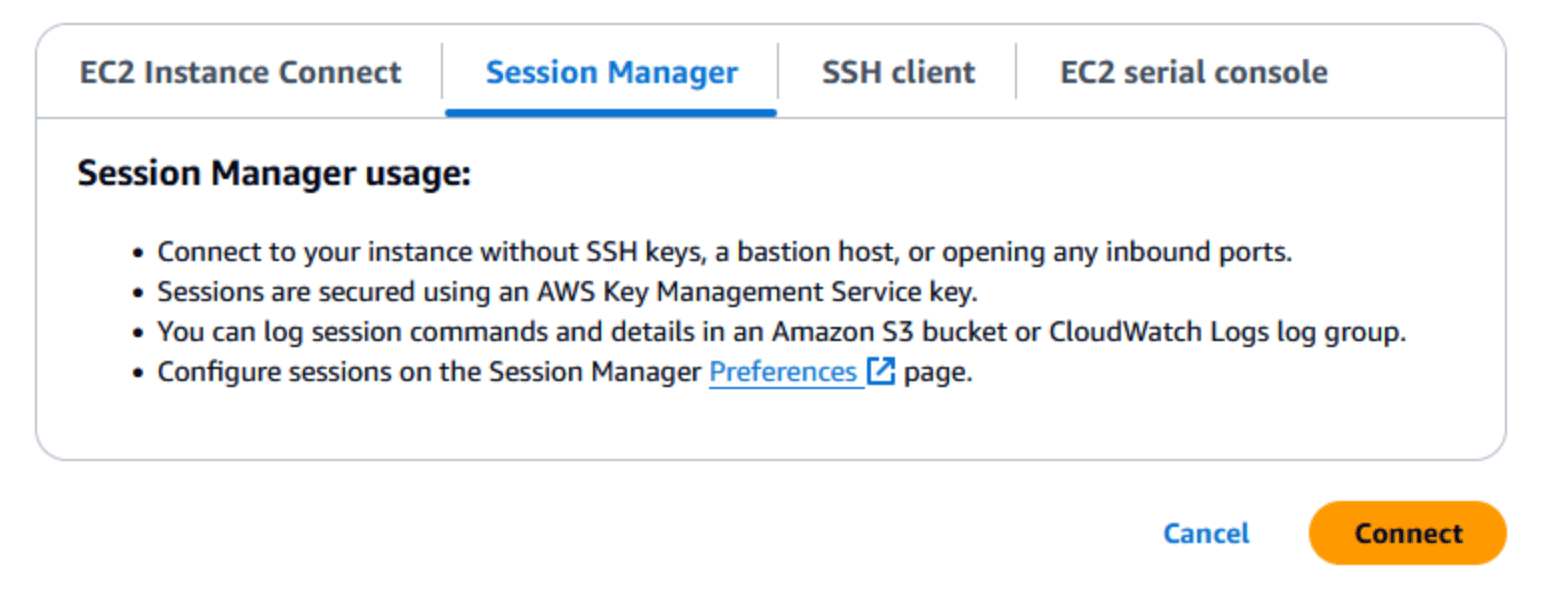
There are other options as well such as EC2 Instance connect and EC2 Serial console but that,s a story for another post! :)